
Cellular POTS Replacement
As the Federal Marketplace continues to evolve, a couple of things…
Cellular Wireless Encryption: End-to-End
As the proliferation of connected devices accelerates a wide…

M2M Two-Factor Authentication @ 30,000 Feet
One of the greatest benefits of the proliferation of Machine-to-Machine…
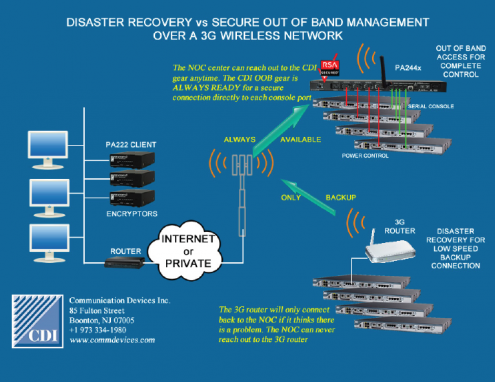
Wireless Disaster Recovery vs. Wireless OBM
The 3G/4G router has become a staple for network operations personnel…

CDI Adds M2M Capabilities to Product Roster
Communication Devices Inc. (CD)I has recently announced that…

POTS Replacement and Security
We've have been getting a lot of calls from businesses looking…

Machine to Machine (M2M) Security
The advent of the ubiquitous wireless device is here, and proof…

What Defines a Full Service MSSP?
The use case for the MSSP has been well documented. Key benefits…

Network Access Control
In order to efficiently operate, business today must build and…

3rd Party Access To Your Company’s Remote Sites
I’ve recently been in talks with clients on the subject of…

2012 The Year of DDOS
I was reading the other day about a fresh wave attacks threatened…

Why RADIUS and TACACS+ Both Fail
Today most router products on the market provide a console/maintenance…
